Unlock the full potential of your digital workspace! Mastering your Cursor Login experience is more than just typing a username and password. It’s about ensuring seamless, secure access to your tools, safeguarding your valuable data, and propelling your productivity to new heights. This comprehensive guide empowers you with everything you need to know, from your first sign in to advanced security measures. Prepare to transform your approach to user authentication and maximize every moment within the Cursor ecosystem.
- Understanding the Cursor Login Process and Authentication Flow
- First-Time Cursor Account Access: A Step-by-Step Walkthrough
- Troubleshooting Common Cursor Login Issues and Error Messages
- Recovering Your Cursor Login Password or Username
- Enhancing Your Cursor Login Security: Best Practices
- Implementing Two-Factor Authentication (2FA) for Cursor Login
- The Benefits of a Seamless Cursor Login Experience
- Managing Multiple Cursor Profiles and Accounts
- Cursor Login on Different Devices and Operating Systems
- What to Do When Your Cursor Login Fails Repeatedly
- Safeguarding Your Cursor Login Credentials from Unauthorized Access
- Best Practices for Maintaining Cursor Login Security
- Frequently Asked Questions About Cursor Login and Account Management
- Future Trends and Updates in Cursor Authentication
- Maximizing Productivity After a Successful Cursor Login
- Frequently Asked Questions
Understanding the Cursor Login Process and Authentication Flow
Ever wondered what happens behind the scenes when you initiate your Cursor Login? It’s a precise series of steps ensuring only authorized users gain entry. When you visit the designated login page and submit your credentials, the system springs into action. First, it securely transmits your input. Next, it verifies these details against its stored records. This user authentication involves cryptographic checks, comparing hashes rather than raw data, adding a crucial layer of security. Upon successful validation, the system generates a secure session token, granting you full access account privileges. This entire flow happens in milliseconds, designed for both speed and ironclad protection.
First-Time Cursor Account Access: A Step-by-Step Walkthrough
Embarking on your Cursor journey begins with a smooth initial setup. Gaining first-time Cursor account access is straightforward. Follow these simple steps to successfully sign in and start using your new tools:
- Visit the Official Platform: Navigate directly to the official Cursor website or application. Look for the “Sign Up” or “Get Started” option.
- Create Your Account: You’ll typically provide an email address, create a strong password, and perhaps enter some basic profile information. Ensure your password is unique and complex.
- Verify Your Email: Check your inbox for a verification email from Cursor. Click the link inside to confirm your email address. This step is vital for security.
- Set Up Your Profile (Optional): Some platforms might prompt you to complete your profile with additional details.
- Perform Your First Cursor Login: Return to the login page. Enter the email address and password you just created. Click “Log In” or “Sign In.”
Congratulations! You now have full access account capabilities and are ready to explore everything Cursor offers.
Troubleshooting Common Cursor Login Issues and Error Messages
Even the most robust systems can present occasional hiccups. If your Cursor Login isn’t going as planned, don’t panic. Many common issues have simple explanations. You might encounter messages like “Invalid Credentials,” “Account Locked,” or “Connection Error.” These usually point to specific problems. An “Invalid Credentials” message often means a typo in your username or password. An “Account Locked” status indicates too many failed attempts, a security measure. Sometimes, a “Connection Error” suggests a problem with your internet link, not the login page itself. Identifying these patterns helps you quickly pinpoint the root cause before seeking more advanced help.
You might encounter messages like “Invalid Credentials,” “Account Locked,” or “Connection Error.” These usually point to specific problems. An “Invalid Credentials” message often means a typo in your username or password. An “Account Locked” status indicates too many failed attempts, a security measure.
Recovering Your Cursor Login Password or Username
Forgetting your Cursor Login credentials happens to everyone. Fortunately, recovering your password or username is a simple, secure process designed to get you back into your account quickly. If you forget your password, look for the “Forgot Password?” link on the login page. Clicking this will typically prompt you to enter your registered email address. Cursor then sends a secure link to that email, allowing you to reset your password. For a forgotten username, the process is similar. Many systems let you retrieve your username by entering your associated email address. Always ensure you are on the official Cursor site when performing these recovery steps to protect your user authentication details.
Enhancing Your Cursor Login Security: Best Practices
Protecting your Cursor Login is paramount. Implementing strong security practices significantly reduces the risk of unauthorized access. Always create unique, complex passwords that combine uppercase and lowercase letters, numbers, and symbols. Avoid using easily guessable information like birthdays or common phrases. Consider a reputable password manager to securely store and generate these strong credentials. Never share your login page details with anyone. Be wary of public Wi-Fi networks when logging in, as they can sometimes be insecure. By following these fundamental steps, you build a robust defense around your account and ensure your access account remains private.
Implementing Two-Factor Authentication (2FA) for Cursor Login
Elevate your Cursor Login security with Two-Factor Authentication (2FA). This critical feature adds an extra layer of protection beyond just your password. When 2FA is active, logging in requires two distinct verification methods. Typically, after entering your password, you’ll receive a unique code via an authenticator app, SMS, or email. You then enter this code to complete the user authentication process. Even if someone discovers your password, they cannot gain access account privileges without also possessing your second factor. Enabling 2FA is a straightforward process within your Cursor account settings and provides invaluable peace of mind against cyber threats.
Even if someone discovers your password, they cannot gain access account privileges without also possessing your second factor.
The Benefits of a Seamless Cursor Login Experience
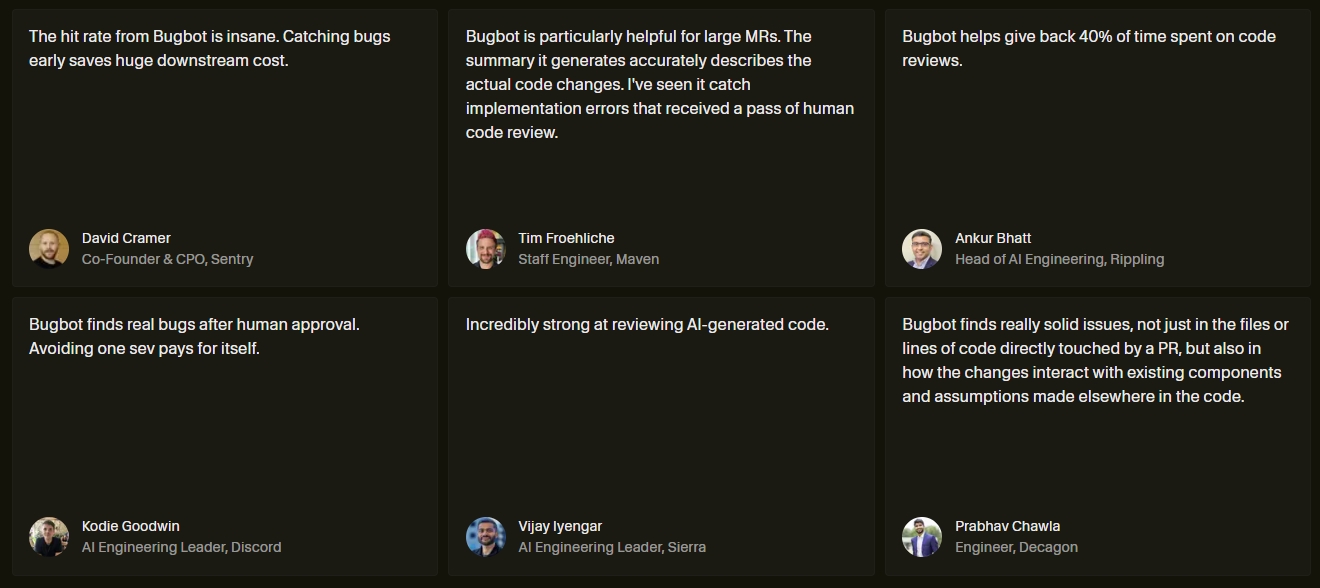
Imagine effortlessly transitioning into your workflow, every single time. A seamless Cursor Login experience brings tangible benefits, directly impacting your daily output. When you can quickly and reliably access account functions, you eliminate frustrating delays and interruptions. This smooth entry minimizes cognitive load, allowing you to dive straight into your tasks with full focus. It boosts overall efficiency, saving precious minutes throughout the day. A frictionless sign in contributes to a more positive user experience, reducing stress and encouraging consistent engagement with the platform. Ultimately, a well-optimized login process translates directly into enhanced productivity and a more enjoyable interaction with Cursor.
When you can quickly and reliably access account functions, you eliminate frustrating delays and interruptions. This smooth entry minimizes cognitive load, allowing you to dive straight into your tasks with full focus. It boosts overall efficiency, saving precious minutes throughout the day.
Managing Multiple Cursor Profiles and Accounts
For power users or those juggling professional and personal projects, handling multiple Cursor profiles and accounts efficiently is key. Successfully managing diverse Cursor Login instances ensures you always work in the correct environment. Many users opt for browser profiles, keeping separate cookies and login sessions for each account. Others use incognito or private browsing windows to maintain distinct sessions without mixing data. Some advanced users leverage password managers with auto-fill capabilities that distinguish between different login page credentials for multiple accounts. Organize your bookmarks and shortcuts to quickly jump to the right account, streamlining your workflow across all your Cursor interactions.
Cursor Login on Different Devices and Operating Systems
Your Cursor Login experience adapts across various platforms, ensuring consistent access account functionality whether you’re on a desktop, laptop, or mobile device. While the core user authentication process remains the same, how you interact with the login page might vary. On mobile, you might experience a touch-optimized layout or utilize biometric login (fingerprint, face ID) if enabled. Desktop applications often provide “Remember Me” options for quicker re-entry. Regardless of your operating system – Windows, macOS, Linux, Android, or iOS – Cursor prioritizes a secure and intuitive experience. Always ensure you are using the official application or website for each device to maintain security.
What to Do When Your Cursor Login Fails Repeatedly
Facing persistent Cursor Login failures can be frustrating, but systematic action resolves most issues. If you’ve already checked your credentials and cleared your browser cache without success, consider these advanced steps. First, try logging in from a different browser or device to rule out a localized client problem. Next, temporarily disable any VPN or proxy services, as they can sometimes interfere with connection to the login page. Check Cursor’s official status page for any reported outages or maintenance. If the problem persists, gather details about the error messages, the device you’re using, and the time the issue started. Then, contact Cursor’s official support team with this information for direct assistance in regaining access account privileges.
Safeguarding Your Cursor Login Credentials from Unauthorized Access
Protecting your Cursor Login credentials is an active, ongoing effort against evolving threats. Beyond strong passwords and 2FA, vigilance is your greatest asset. Be extremely cautious of phishing attempts: fraudulent emails or websites designed to trick you into revealing your user authentication details. Always double-check the URL to ensure you are on the legitimate login page. Never click suspicious links. Avoid writing down passwords in unsecured locations. Regularly review your Cursor account activity for any unfamiliar logins or actions. By staying alert and proactive, you significantly reduce the risk of unauthorized individuals gaining access account privileges.
Best Practices for Maintaining Cursor Login Security
Sustaining robust Cursor Login security requires consistent attention. It’s not a one-time setup, but an ongoing commitment. Regularly update your password, ideally every few months, ensuring each new password is distinct from previous ones. Always keep your browser and operating system updated to their latest versions; these updates often include critical security patches. Periodically review your account settings for any authorized devices or connected applications you no longer use, and revoke their access. Staying informed about common cyber threats and security news also helps you react quickly to new risks. This proactive approach ensures your user authentication remains strong and your access account secure against evolving threats.
Frequently Asked Questions About Cursor Login and Account Management
We’ve gathered common inquiries to provide quick answers regarding your Cursor Login and account management.
- Q: What if I forget my username?
A: Most platforms allow you to retrieve your username by entering your registered email address on the login page‘s “Forgot Username” link. - Q: Is my Cursor Login secure on public Wi-Fi?
A: It’s generally not recommended. Public Wi-Fi networks can be unencrypted and vulnerable to eavesdropping. Use a VPN for added security if you must sign in. - Q: How do I change my profile picture?
A: Navigate to your account settings or profile management section within Cursor after a successful sign in. Look for an “Edit Profile” or “Change Avatar” option. - Q: Can I merge two Cursor accounts?
A: This functionality varies by platform. Check Cursor’s support documentation or contact their team directly to inquire about merging or transferring data between accounts.
For any specific issues, always consult Cursor’s official help resources after you access account details.
Future Trends and Updates in Cursor Authentication
The landscape of Cursor authentication is constantly evolving, promising even greater security and convenience for your login page experience. We anticipate a surge in passwordless solutions, moving beyond traditional passwords to methods like FIDO2 security keys, advanced biometrics (fingerprint, facial recognition, voice), and magic links sent to trusted devices. AI and machine learning will play an increasingly vital role in real-time threat detection, identifying unusual login patterns or locations to prevent unauthorized access account attempts before they even occur. Expect a future where your Cursor Login is not only more secure but also dramatically simpler, seamlessly integrating into your digital identity with minimal friction.
Maximizing Productivity After a Successful Cursor Login
Your successful Cursor Login is just the beginning; the real power lies in how you leverage the platform. Immediately after you access account features, dive into optimizing your workflow. Explore Cursor’s shortcuts and integrations to streamline repetitive tasks. Customize your dashboard to display the most relevant information for your current projects. Set up notifications strategically to stay informed without being overwhelmed. Take advantage of collaboration tools to connect efficiently with your team. By consciously integrating Cursor’s capabilities into your daily routine right after you sign in, you transform mere access into a launchpad for unparalleled enhanced productivity.
Frequently Asked Questions
How does the Cursor Login authentication process work?
When you submit your credentials, the system securely transmits and verifies them against stored records using cryptographic checks. Upon successful validation, a secure session token is generated, granting you access.
What are common issues encountered during Cursor Login and how can they be identified?
Common issues include “Invalid Credentials” (often a typo), “Account Locked” (too many failed attempts), or “Connection Error” (internet problem). Identifying these messages helps pinpoint the root cause.
What steps should I take if I forget my Cursor Login password?
Look for the “Forgot Password?” link on the login page, enter your registered email address, and follow the secure link sent to your email to reset your password.
Why is Two-Factor Authentication (2FA) crucial for Cursor Login security?
2FA adds an essential layer of protection by requiring a second verification method (like a code from an app or SMS) after your password, ensuring unauthorized users cannot access your account even if they know your password.
What are best practices for maintaining strong Cursor Login security?
Always use unique, complex passwords, consider a password manager, be cautious on public Wi-Fi, never share login details, and stay vigilant against phishing attempts.